In our discussions of custom CMS solutions and how they compare to off-the-shelf options like WordPress, we consistently run into the question of security.
As the CMS with the largest market share, WordPress is a big target for hacks. Running your site on WordPress comes with a responsibility to run updates—especially security updates—as soon as they come out.
And to their credit, WordPress is pretty good about releasing updates. In the past year, they released a number of security updates soon after being made aware of certain vulnerabilities, even on fairly short notice.
But what happens when the WordPress team chooses not to fix an issue,or considers it low enough priority that it can be delayed?
A few weeks ago, I received a puzzling email from one of our clients. She had received a number of password reset emails that she had not requested. We checked the password reset links in the email and they were legitimate.
The interesting part is that they were not “from” the website.
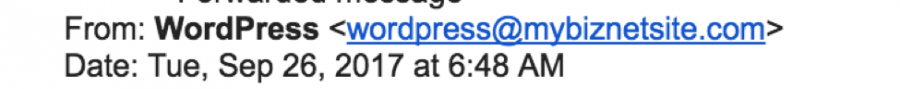
It’s worth noting that MyBizNetSite.com is not a client of NPG, nor have they ever been.

What’s the Problem?
The link isn’t spam or malware.
The email went to an actual website admin with a legitimate account.
So what really went wrong here? And does it matter that the email looked like it came from a random email address?
Yes, it does. And it appears WordPress would agree.
WordPress defines security issues as bugs that can allow unauthorized access to a site. On their instruction manual for reporting vulnerabilities, they write:
“If you get an email saying “Someone has asked to reset the password for the following site and username”, this means someone visited the password reset page on your site. Anyone can visit this page, since it must be open to all for it to be accessible to those who have lost their password. Your password can be reset only by those who can read your email. If your email account has not been compromised, you can ignore this email.”
Case closed? Not quite.
A Low-Priority Bug?
Security researcher Dawid Golunski publicly reported this vulnerability in March 2017, detailing how an attacker can force WordPress to send legitimate password reset emails with a malicious “From” value.
Though it seems harmless, Golunski details several different scenarios in which this could lead to the attacker gaining possession of the password reset link (and therefore gain access to the admin account):
- The attacker could send a large number of emails to the user as a kind of denial of service (DoS) attack, prompting the emails to bounce back to the faked “from” email address.
- If the recipient’s email address has an auto-reply, it might include a copy of the original email in the body of its autoresponse.
- After receiving many password reset emails in a short amount of time, the user might reply to the emails to express annoyance or at least request an explanation. Most email replies also include the body of the initial message.
A review of our logs showed that this is likely what the attacker on our client’s site was trying to do. There were nearly 20 reset emails sent to a single user within a single hour.
While this may sound like a convoluted case of social engineering, two of those scenarios can take place without any action taken by the email recipient. We were able to quickly patch this on the server level, but others may not be so lucky.
It appears that WordPress may consider this unlikely or overblown. The bug was first reported to them in July 2016 and only publicized by Golunski after nearly a year without a patch.
A Custom Solution
So, is your WordPress site in danger now?
Probably not. Depending on whether your site is on a shared or dedicated server, you may not be vulnerable at all (and there are available defenses via server configuration). The security experts at WordPress may also be correct that there time is better spent on other more pressing vulnerabilities that have been found in the past year.
However, building a custom CMS solution protects you (at least) twice over in any of these scenarios! By avoiding the most popular CMS platform in the world, you don’t have to worry about being part of the biggest target. You also have access to concepts like a decoupled or headless CMS, separating out a website’s display layer from its content management system and hiding your administrative tools from common hacks and viruses.
More importantly, your fate is in your own hands with a custom CMS. If a vulnerability does come to your attention, you don’t have to wait around for a fix, nor do you have to defer to someone else’s assessment of the level of risk.



